43332
|
Author | Wu Shuo Blockchain by calling contract 0x00000000000000000000000000000000001006 (BSC: Relayer Hub) at block height 21955968 According to the initial timeline compiled by Supremacy: At 00:55 on October 7, 2022 Beijing time, the hacker reached the block height 21955968 By calling contract 0x000000000000000000000000000000000001006 (BSC: Relayer Hub), pay 100 BNB to register as a relayer. 02:26 points hacker at block height 21957793 An attack was launched by calling contract 0x000000000000000000000000000000000002000 (BSC: Cross Chain), and the attack profit was 1 million BNB. 04:43 points hacker at block height 21960470 The attack was launched again by calling contract 0x0000000000000000000000000000000000002000 (BSC: Cross Chain), and the attack once again made a profit of 1 million BNB. The hacker obtained (cast out of thin air) a total of 2 million BNB from the BNB Chain Token Hub system contract in two times, and mortgaged 900,000 BNB on the BNB Chain lending agreement Venus, lending 62.5 million BUSD, 50 million USDT, and 35 million USDC. Supremacy said that as of the time of publication, we believe that there is a problem with BSC's Merkel tree verification, and the analysis is still in progress. According to Paidun, BNB Chain attackers have transferred approximately $89.5 million in stolen funds to other chains (non-BNB Chain), with approximately 58% of the funds transferred to Ethereum, approximately 33% of the funds transferred to Fantom, and approximately 4.5% of the funds transferred to Arbitrum. Tether quickly blacklisted 4.8 million USDT on Ethereum (and subsequently blacklisted 1.7 million USDT on AVAX). BNBChain announced that it will suspend the chain. “We ask BSC validators to contact us in the next few hours so we can plan node upgrades. ” CZ said that BSC Token Hub is the bridge between the BNB beacon chain (BEP2) and the BNB chain (BEP20 or BSC). The current amount affected is estimated to be approximately $100 million. Analysts pointed out that although the timely suspension of BNBChain resulted in a small amount of outflow, it will also face an embarrassing situation in the future. If hackers do not take the initiative to deal with it, the issue of how to deal with the amount remaining in BNBChain will inevitably trigger a centralization/decentralization controversy. Yu Xian, founder of SlowMist, commented: From the perspective of theft methods and currency laundering methods, this wave of hackers acted quickly and accurately. You may not have expected that Binance would also act very quickly and accurately (suspending BSC and teaming up with Tether and others to freeze related funds). "This wave of hackers is not simple... Let’s see if we can trace the identity of the hackers this time.” However, the Chinese community has also criticized this because BNBChain did not choose a similar centralized approach to the previous coin theft cases. According to SlowMist, the original source of the hacker's funds was ChangeNOW, and the hacker's address had interacted with multiple DApps, including Multichain, Venus Protocol, Alpaca Finance, Stargate, Curve, Uniswap, Trader Joe, PancakeSwap, SushiSwap, etc. 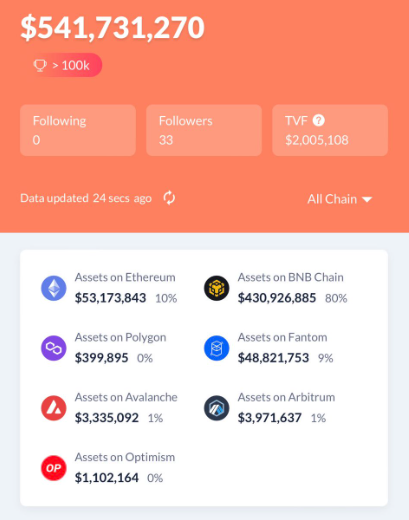 (Current profit distribution of hackers, from SlowMist) 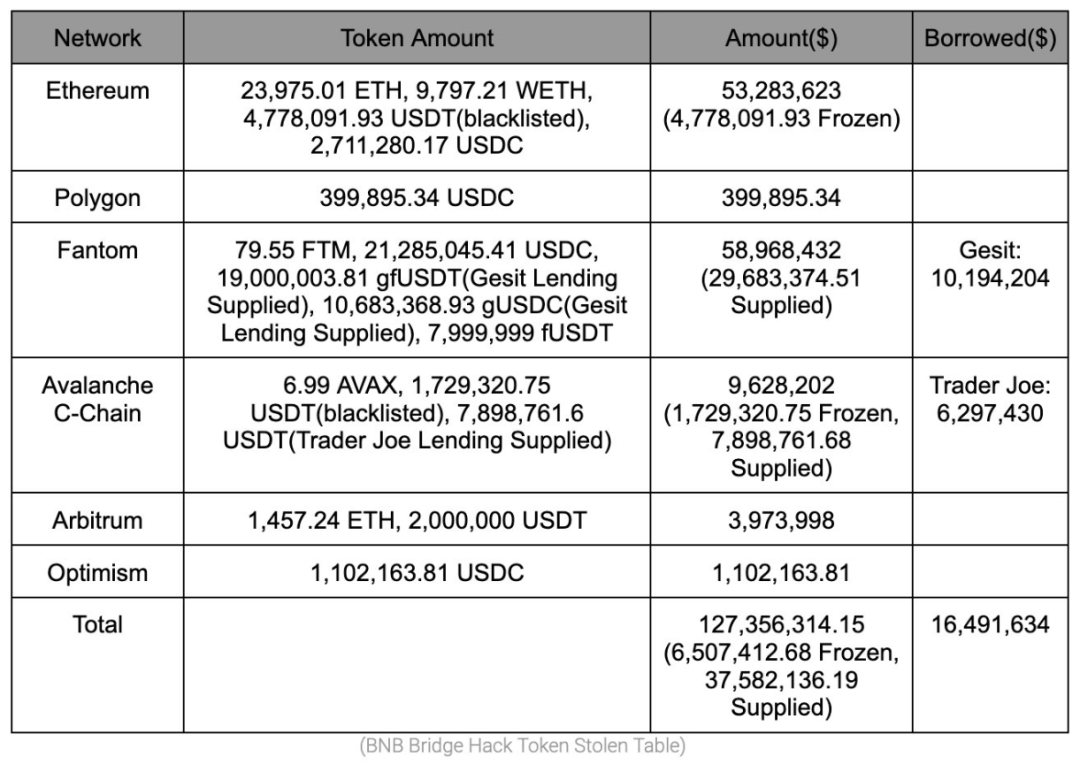 Analyst @samczsun posted an article explaining how hackers used Binance Bridge to steal BNB. The attacker stole 1 million BNB twice, but the height used was 110217401, which is far lower than the normal height. Furthermore, the proof submitted by the attacker is shorter than the legitimate proof, indicating that the attacker forged the proof for this particular block. The specific method is to add a new leaf node when the COMPUTEHASH function generates the hash, then create a blank internal node to satisfy the prover, and exit early after finding the hash that matches the internal node. So far, there are only two pseudo-verifications generated in this way. "In summary, there is a bug in the way Binance Bridge validates proofs that could allow an attacker to forge arbitrary messages. Fortunately, the attacker here only forged two messages, but the damage could have been much more severe." The incident is still developing. For more updates, please follow the Wushuo Telegram channel and Chinese Twitter, or the official website update URL: https://www.wu-talk.com/index.php?m=content&c=index&a=show&catid=46&id=8367    Welcome to read the selected reports of Wu Shuo: exclusive reports on Huobi, exclusive reports on Binance, Bitmain series, supervision and card freezing series, Filecoin series, exposure of chaos in the currency circle, mining supervision trends, etc. (Due to the adjustment of the official account push logic, old readers please add a star to the Wu Shuo official account to avoid being unable to receive it. How to add stars: How to set a star for the official account) According to the "Notice on Further Preventing and Dealing with Speculation Risks in Virtual Currency Transactions" issued by the central bank and other departments, the content of this article is only for information sharing and does not promote or endorse any business or investment activities. Readers are requested to strictly abide by the laws and regulations of their region and not participate in any illegal financial activities. It does not provide transaction entrances, guidance, issuance channel guidance, etc. for the issuance, trading and financing related to any virtual currency or digital collections. Wu said the content is prohibited from reprinting or copying without permission, and violators will be held legally responsible. |