36119
 Recently, researchers from the Israeli network security company JSOF discovered that the Treck TCP/IP protocol was affected by a total of 19 0day vulnerabilities, so they called this vulnerability Ripple20.  Source: FreeBuf Cyber Security Industry Portal JSOF also warned that due to serious security vulnerabilities affecting the Treck TCP/IP stack, hundreds of millions (or even more) IoT devices around the world may be subject to remote attacks. This vulnerability affects a variety of industries, affecting home/consumer devices, healthcare, data centers, enterprise, telecommunications, oil, gas, nuclear energy, transportation, and many other critical infrastructures.  Vulnerability scope Source: FreeBuf Cyber Security Industry Portal The impact of the Ripple20 vulnerability is fierce and affects the world. Billions of Internet-connected devices, from consumer products such as printers and IP cameras to specialized equipment used across organizations (such as video conferencing systems and industrial control systems, etc.) are all at risk of attack. Strengthening the security protection of IoT applications is crucial. Ripple20 vulnerability strikes, how does Sundray IoT ensure application security?  Sundray IoT provides comprehensive security guarantee As a subsidiary of Sangfor Group, Sundray Technology has network security genes and has passed CMMI Level 5 certification. The software has stable and mature features and can meet the relevant requirements for IoT security in Class A Protection 2.0. At the same time, Sundray Technology's IoT products mainly use LoRa, ZigBee, 433, modbus/485 and other protocols in the perception layer. The transmission layer and platform layer all use the self-developed TCP/IP protocol library to ensure that Sundray IoT products are not affected by the Ripple20 vulnerability! Recommended reading: Ripple20 vulnerability exposed, no Sundray products are affected In addition, in terms of security construction, Sundray IoT uses a variety of technical means to ensure the security of personnel access, authority management, data use, and data transmission.  Terminal management identity authentication In terms of access security, Sundray IoT adopts terminal authentication and identity binding methods to manage the identity permissions of access personnel, so that only legally certified managers can access the system for IoT device management. At the same time, dual protection is provided at the device layer and gateway side to avoid security risks of illegal access by unauthorized personnel.  Access personnel identity management 1. Device layer identity security guarantee One device, one secret: One key for each device, and identity verification is performed when connecting. 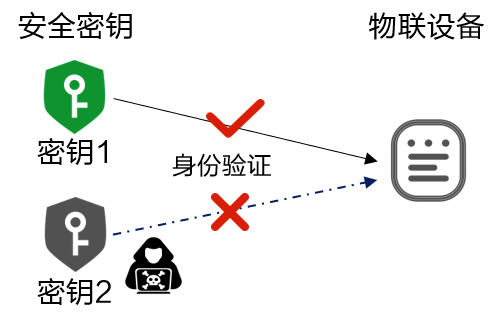 One type, one secret: One key for each device type, and identity verification is performed during connection.  Continuous encryption: Each time a session is established, the session key is recalculated using the above key. 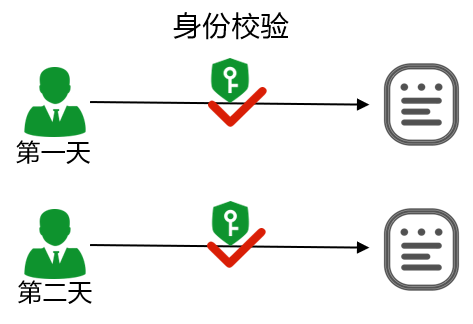 Anti-phishing: Prevent customer A’s terminal from being phished by customer B and manage it on its own gateway. 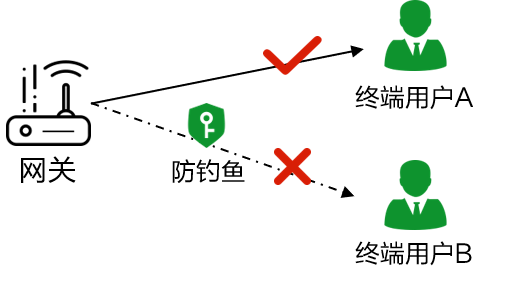 Gateway identity verification: The terminal verifies the gateway identity every time data is exchanged to prevent connecting to other gateways.  2. Identity security on the gateway side Terminal identity verification: data filtering to prevent problematic data from attacking the platform through the gateway  Device black and white list: Set which terminals are allowed/not allowed to connect.   Classification and decentralization of management personnelIn the process of daily operation, maintenance and management, unclear authority of managers can easily lead to the risk of data leakage. For example, third-party maintenance personnel and branch personnel can view data at the group headquarters or outside their authority, leading to increased security problems. Sundray IoT Computer Room Sentinel can assign different management rights according to the different responsibilities of managers to ensure data security.   Platform intranet deploymentIn the construction of traditional computer room dynamic environment, if APP is used for remote management, the system platform must be open to the public network and directly deployed to the public network or continue port mapping, which brings greater risks to data storage. In response to this situation, Sundray IoT has created an original intranet deployment method to realize remote management and remote cloud protection functions of the APP. At the same time, the platform itself only needs to be online online, reducing the risk of data leakage.  Data encrypted transmissionIn terms of data transmission, in order to ensure data security, data transmission between the mobile APP and the platform uses a dedicated key to protect the data from external cracking and interception. When remote cloud guardian is enabled, the type of uploaded data is determined by the user. If only alarm data is uploaded, other data will not be uploaded simultaneously, which greatly ensures the transmission security of key data.  Data transmission security With the development of IoT technology, more and more users have established multi-scenario IoT applications. With the emergence of the Ripple20 vulnerability, hundreds of millions of IoT applications around the world are exposed to potential attacks. Strengthening the security of IoT applications will be a key focus of future IoT development. Sundray Technology will continue to innovate and explore to protect the security of your IoT applications. If this article is useful to you Welcome to forward to Moments Click on the title below to read more Enterprise-level wireless: Is Wi-Fi6 very good? | Wireless animation | Wireless security | Wi-Fi6 flagship | Wi-Fi6+X-LINK dual-line transmission | [Ruiman Talk] Xiao Zhao is poisoned | [Ruiman Talk] East-West Traffic 2.0 | [One Picture Communication] Government Wireless ATV switch: quick start in 7 minutes and 01 seconds | ATV switch status visibility | ATV switch quick start | ATV switch minimalist operation and maintenance | East-West traffic 2.0 | Intranet security within Class 2.0 Enterprise-level IoT: DingTalk + IoT | SDC software-defined classroom | Sentinel speed package | IoT ecosystem | Understand the computer room Sentinel with one picture | Understand network equipment monitoring with one picture | Spring Silkworm campus animation video | Computer room Sentinel animation video Industry solutions: Smart campuses for primary and secondary schools | [YiTuTong] smart warehousing | [YiTuTong] smart stores | [YiTuTong] smart hospitals | [YiTuTong] government office wireless | Internet finance | Information-based "three no's" hospitals Event Express: Campus Network Quick Start Challenge | Partner Cloud Recruitment Conference | Sundray Technology Annual Conference Special | Change to create a better future together! | International Partner Conference | The 77th China Educational Equipment Exhibition   |