76497
 Reply to "Resources" to receive the 30G marketing planning package Reply to "Community" to enter the Mr. Virus official fan group Although we can still feel the cold wind from the blockchain industry in this midsummer season, it does not prevent us from thinking about the opportunities of an emerging industry. For the booming blockchain industry, we see that the track chosen by most entrepreneurs is the direction of blockchain + industry applications, which is highly dependent on basic public chains like Ethereum. However, it is also limited by the fact that these public chain technologies are still in their infancy, and the entire industry is still very weak in terms of practical applications. Due to the high technical difficulty of the public chain track, few teams have participated in the competition. As a star player who claims to surpass ETH and beat EOS, what is the design logic of IOST's public chain? Today, sir, I will reveal it to you one by one. IOST is a blockchain platform for distributed applications. Centralized platforms have dominated for so long that people have forgotten that there is a better way to build internet services. IOST is an effective way to develop a community-owned network and can provide a platform for third-party developers, creators, and enterprises to realize value. IOST's solution is actually to solve the triangular conflict of scalability, rather than to avoid solving the problem by sacrificing censorship resistance. While trying various scalability solutions, the IOST blockchain has always maintained its censorship resistance, open participation, and protection from malicious attacks. IOST is more decentralized than EOS and more scalable than ETH. IOST has the following 5 characteristics
1Censorship Resistance 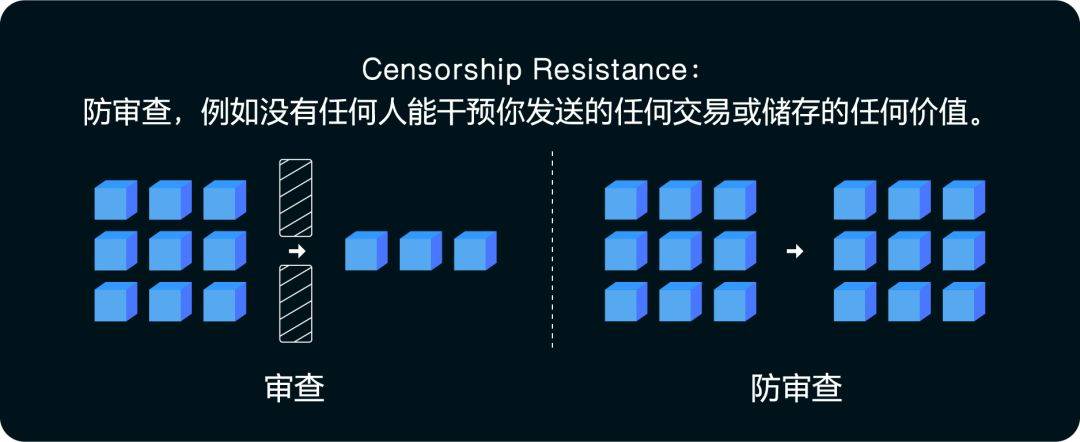 IOST attaches great importance to decentralization, especially maintaining proper censorship resistance while expanding its capacity. While trying various scalability solutions, the IOST blockchain always maintains its censorship resistance, open participation, and protection from malicious attacks, no matter how powerful the scalability is. Every node on the IOST chain will have an equal opportunity to be elected to the committee to participate in verifying transactions and producing blocks. IOST will not sacrifice its censorship resistance capabilities. Many people say that when blockchain is finally successfully implemented and widely used, these networks must have throughput that can compete with networks like Visa. No one wants to use an application that takes days, hours, or even seconds to interact with. This is a very one-sided view. This conclusion is correct to a certain extent. Blockchain needs to have performance comparable to centralized services, but it does not emphasize that performance improvement cannot be based on the premise of sacrificing decentralization. Most people do not realize the fundamental value that blockchain provides - Censorship Resistance. If the blockchain does not have the characteristics of censorship resistance, but relies on a fixed group of nodes to produce blocks like EOS, then we have just returned to the traditional centralized database, and it does not yet have the efficiency that Amazon Web Services and Microsoft Azure Cloud can provide. Why is Censorship Resistance important? The censorship resistance feature of the Bitcoin blockchain means that anyone can own the value of Bitcoin without the risk of being deprived of it by malicious actors such as institutions or managers. The value of Censorship resistance is not only reflected in monetary assets. The design of the IOST blockchain reflects this. Instead of static nodes, IOST has a dynamic, reputation-based committee that verifies transactions and generates blocks. Every node in the blockchain has a fair chance to be elected to the committee. IOST allows developers to create censorship-resistant applications and smart contracts. If you enter a smart contract with other users, it is important to know the rules of the smart contract and that any records cannot be tampered with at your expense. When your identity information, such as social security account number, credit status and other information is stored and processed by smart contracts, it is very important to be sure that no malicious persons have tampered with your information. Some DPOS supporters claim that blockchains based on DPOS are censorship resistant. However, censorship has already started after the EOS mainnet went online. “The EOS Core Arbitration Forum (ECAF) is a newly established centralized organization that ordered all blockchain producers on the chain to freeze 27 accounts on the network. Following the move, they said: "The logic and reasons for issuing this order will be announced at a later date. ” This order was issued by a person named Sam Sapoznik, and no supernode raised any questions after the order was issued. Without censorship resistance, there is no point in using blockchain because decentralization is gone and anything on the blockchain can be compromised. So far, some new content has been added to the EOS blockchain terms. The new terms do not include any decentralized decision-making process. This gives the EOS Core Arbitration Forum (ECAF) unlimited discretion to make some binding decisions. EOS censorship is already buried in the terms. This familiar centralized management has run counter to the original purpose of digital currencies when they were created. 2Algorithmic Election Committee The IOST blockchain uses an algorithm to select the verification committee based on their contribution to the community and token holdings, rather than using an on-chain voting system like most blockchains based on the DPOS mechanism. On-chain voting selection committees are seriously flawed. This mechanism attempts to replicate the conditions of representative democracy, but to quote Vitalik, the 1-person-1-vote system of representative democracy has been replaced by a 1-coin-1-vote system. Such a system would undoubtedly eventually evolve into a plutocracy. People with more capital vote to defeat nodes that are less wealthy than them, so that nodes with less electoral power become increasingly indifferent because their votes have little or no impact on the outcome of the election. Judging from the history of blockchain development, blockchains managed by manual voting mechanisms have less than 15% of participants, such as DAO carbonvote, EIP186 carbonvote, DAO proposal voting, Bitshares DPOS voting in 2014, etc. In the IOST system, the Block Producers (BPs) committee performs algorithmic distribution based on contributions and balances, and each node has the same responsibilities and rights. At the same time, the "tragedy of the commons" may also occur with blockchain voting. 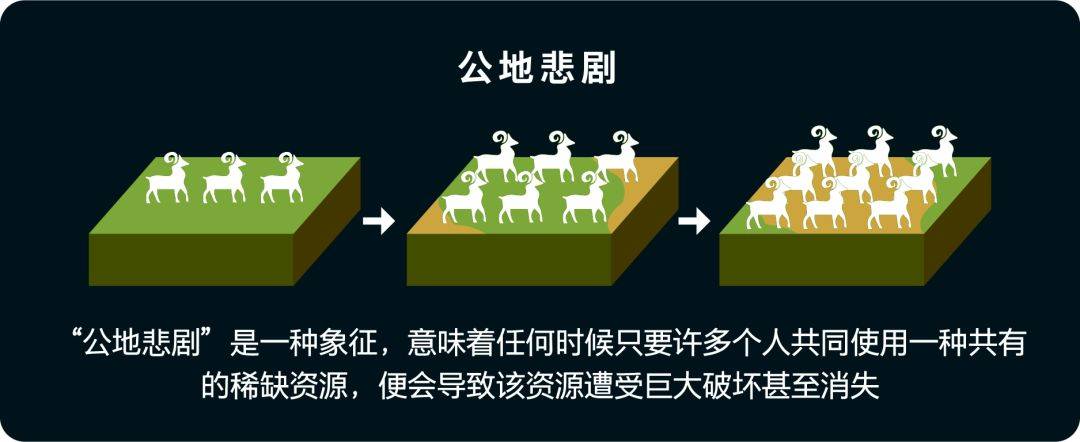 Since each voter has a small chance of influencing the outcome of the vote, their incentive to vote is thousands of times less than ideal. This means that what is likely to happen is that everyone puts their tokens on an exchange and the exchange votes on their behalf, and these users don't really care how the exchange votes with their money. This situation leads to a tendency toward voting centralization. Another problem is that voters gradually accept bribes from block producers BPs (that is, super nodes in DPOS), who receive their annual rewards by buying votes. BPs collude with each other to determine the proportion of spoils between themselves and voters. Because there are incentives for super nodes to buy votes, once elected, all super nodes want to continue to be in power. Therefore, the existence of an incentive to maintain the established order means that the elected supernodes will form an alliance to vote for each other. Lisk, for example, uses a voting system similar to EOS, which results in the blockchain being monopolized by two very powerful mafia-like alliances: Elite and GDT. IOST, on the other hand, uses a dynamic committee model to verify and produce blocks, which prevents the formation of alliances. If a node has just generated a block, the node needs to "cool down" for a period of time before it can participate again. Once similar alliances are formed, the decentralized nature of blockchain platforms will cease to exist. These alliances can even exploit businesses running on EOS in a variety of ways. Participants have to abide by the rules of these interest groups or pay money or risk having their transactions scrutinized. Worse, these reviews are conducted under the table. These super nodes can make certain businesses more difficult to run by changing network logic. In the end, the decision-making power of what can and cannot be done in the network will be in the hands of these super nodes. By censoring in an indirect, hidden way, any possible popular backlash is minimized. After all, the only thing the supernodes need to do is provide a reasonable explanation for why the protocol was modified. As long as the reasons are sound enough, they'll basically be able to get away from the unsuspecting public, and we won't even know if they're running any racketeering operations. 3Equal distribution of economic rewards In Proof of Stake (POS), having more coins and holding them longer will have a greater chance of packaging the next block. Although computing power has been saved compared with Proof of Work (POW), the richer nodes will gain wealth faster than other nodes. The Proof of Believability (POB) system of the IOST blockchain not only rewards nodes with a certain account balance, but also considers how much the node has contributed to the community. Community contribution currently includes the number of transactions verified by nodes and the number of transactions participated in. In the future, the corresponding node's computing power contribution and resource contribution will be increased based on the results of the IOST test network. This means that these groups that actively promote the construction of the IOST network and contribute to it can be rewarded, which means that the right people will be rewarded. In the IOST network, the contribution of nodes will be measured in a unit called Servi. A user's credibility score is determined by both his Servi balance and his token balance. The higher the credibility score, the more likely you are to be selected for the committee. A unique design of the Proof of Believability (POB) consensus mechanism is that Servi will self-destruct. This means that after a node verifies and produces a block, the system will automatically clear the node's Servi balance to zero. Therefore, all nodes will take turns verifying blocks in order of high or low credibility scores, and nodes with high credibility will be constantly replaced due to the destruction of Servi, which ensures equal distribution of block rewards. 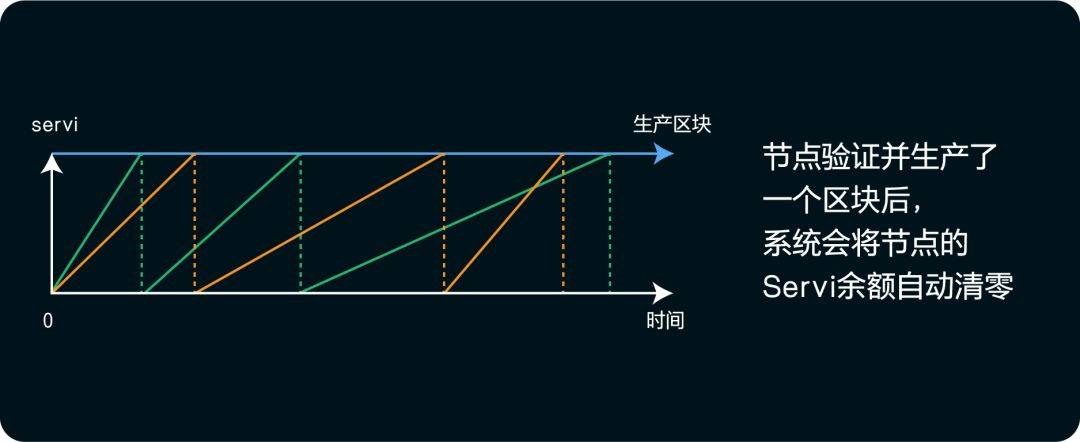 The advantage of the Proof of Believability (POB) consensus mechanism is that it can achieve a more equal distribution of economic incentives. Every user who contributes to the community has an equal opportunity to obtain IOST. More importantly, new members who join the network have the same chance of receiving financial rewards as older members who have been members of the network for a long time. The significance of the Proof of Believability (POB) consensus mechanism is that it gives everyone equal opportunities. IOST is committed to giving ordinary people more reasonable economic incentives and creating a blockchain that provides opportunities for all people. Nodes are no different, everyone can become a super node by contributing. The entire IOST system aims to provide equal and fair opportunities to all participants. 4. Security design of Proof of Believability (POB) The Proof of Believability (POB) consensus mechanism extends the traditional POS, that is, nodes need to accumulate a large number of tokens to be eligible to participate in the creation of a new blockchain and determine the probability of producing blocks based on a certain numerical ratio. In POS, this value is the total amount of tokens accumulated or assigned to a node, while in Proof of Believability (POB), this score includes more variables. Applying the mathematical calculation ideas of network clustering and page ranking, the credibility score is mainly determined by the following factors:  Verification transaction volume: How many transactions the node has verified in the past 30 days. The more recent transactions, the greater the weight.;  Net trading volume: how many transactions were completed in the past 30 days, the more recent the transactions, the greater the weight.;  Token Deposit The token deposit bound to create a new block;  The account of a cluster node at the center node of the network has a slightly greater weight than the account at the edge node of the network. Trustworthiness Score Addresses Two Major Pitfalls of POS One is that nodes simply accumulate as much virtual currency as possible and win rewards from block production: this will concentrate the wealth within the platform and hinder the circulation of IOST. In the POB consensus mechanism, it means that blindly accumulating wealth without helping to produce and disseminate transactions will lead to a lower credibility score. Helping the circulation of IOST can increase credibility. The second is the nothing-at-stake problem: Since block creation does not require resources, when a fork occurs, nodes can freely create new blocks on both forks, which will greatly or infinitely extend a certain fork. Proof of Believability (POB) can prevent this from happening using a "bound deposit" backed by a deposit. As mentioned above, each node’s credibility score includes the user’s staked tokens. In order to be able to unlock these bound token deposits, users must first initiate the unlocking deposit process and then wait for a longer period of time, the so-called 'unbinding period'. This also lets all users know in advance how the verification committee will change. Without this "unbinding period", nodes would be vulnerable to attacks from the original verification committee, which may in fact no longer exist. 5Scalability As discussed earlier, for blockchain to be finally accepted by the mainstream public and realize its revolutionary value, scalability is essential. However, the implementation of blockchain scalability cannot sacrifice censorship resistance, otherwise the blockchain will degenerate into a centralized database. IOST's solution is actually to solve the triangular conflict of scalability, rather than to avoid solving the problem by sacrificing censorship resistance. We improve scalability through protocol-level and Layer-2 extension solutions, including: state channels, sharding, and sidechains. 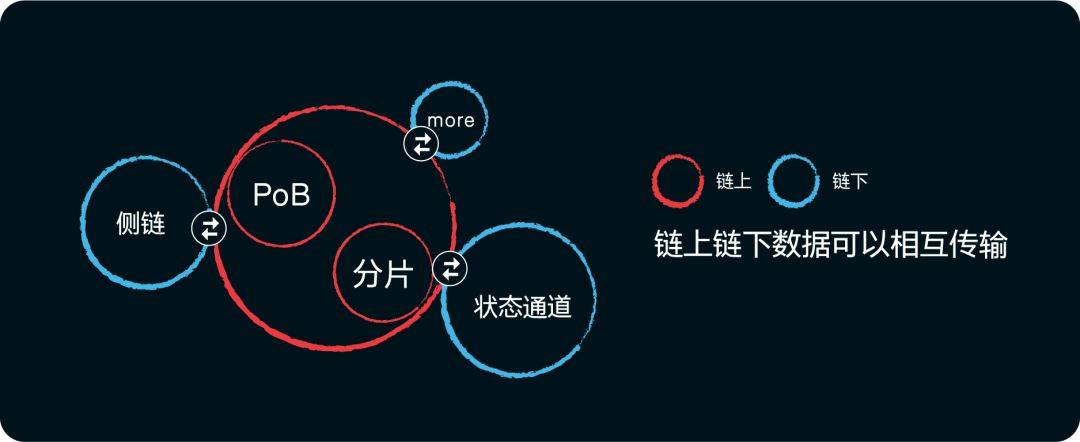 Generally speaking, Protocol-level and Layer-2 are the two main ways to improve the scalability of blockchain. The protocol layer involves building a better-designed underlying blockchain protocol that maintains the expected decentralization and security properties of most blockchains, as we have seen already in existing simple blockchain designs. It requires only a small proportion of nodes to see and process each transaction, and allows many more transactions to be processed in parallel at the same time. The second layer protocol (Layer2) consists of creating an off-chain protocol that sends most transactions off-chain and only occasionally interacts with the on-chain layer to enter and exit from the Layer-2 system. This is also suitable for defending against attacks on the system. We believe that these two strategies are complementary to each other, and we support the adoption of a multi-pronged strategy to improve the scalability of IOST, that is, allowing these two strategies to connect with each other and complement each other's advantages. Through the above description, I believe everyone has a certain understanding of the technical logic of IOST. Here is a brief summary: In response to the iron triangle of mutual constraints faced by the current blockchain underlying architecture, that is, the incompatibility of the three characteristics of security, scalability and decentralization, IOST has proposed innovative solutions such as high-speed distributed sharding (EDS), PoB consensus mechanism and micro-state block (MSB), aiming to create a public chain that is both safe and highly scalable.   |