70496
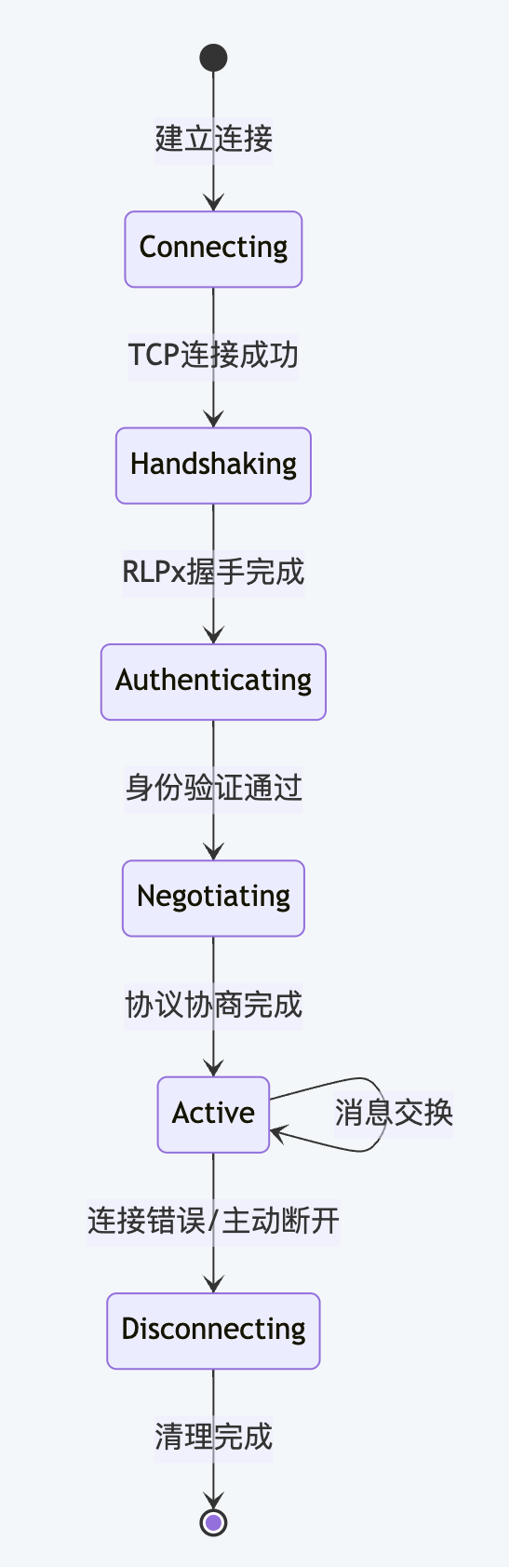
Chapter 1: The need for a decentralized networkAs a decentralized blockchain network, Ethereum's P2P network layer is responsible for the key missions of realizing direct communication between nodes, supporting dynamic expansion and contraction of the network, ensuring the synchronization and consistency of the entire network's blockchain status, and preventing various network attacks and malicious behaviors. It provides the entire blockchain system with a flexible network infrastructure that does not require a central server. 1.2 Overall architecture layered designThe Go-Ethereum P2P network adopts a classic layered architecture design: ┌─────────────────────────────────────────────────────────────────┐Chapter 2: P2P Core Implementation2.1 Architecture designP2P Server adopts a highly optimized event-driven architecture design to receive and process different types of events through multiple dedicated channels, effectively avoiding complex state management and lock competition issues. The system designs each functional module (node discovery, connection dialing, network monitoring, etc.) as independent components and interacts through standardized interfaces, achieving good component decoupling. In terms of concurrency safety, the system gives priority to using channels for communication between components, which not only ensures thread safety but also maintains high-performance concurrent processing capabilities. 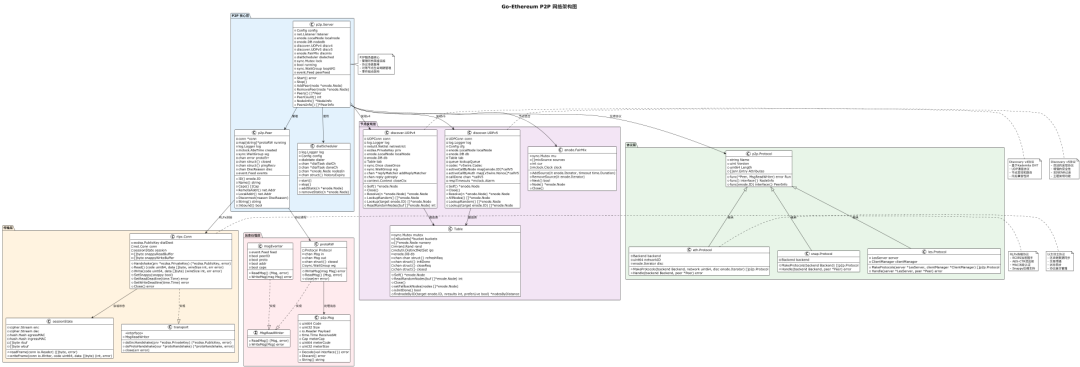 life cycle management mechanismServer life cycle management follows strict state transitions to ensure system stability and reliability: 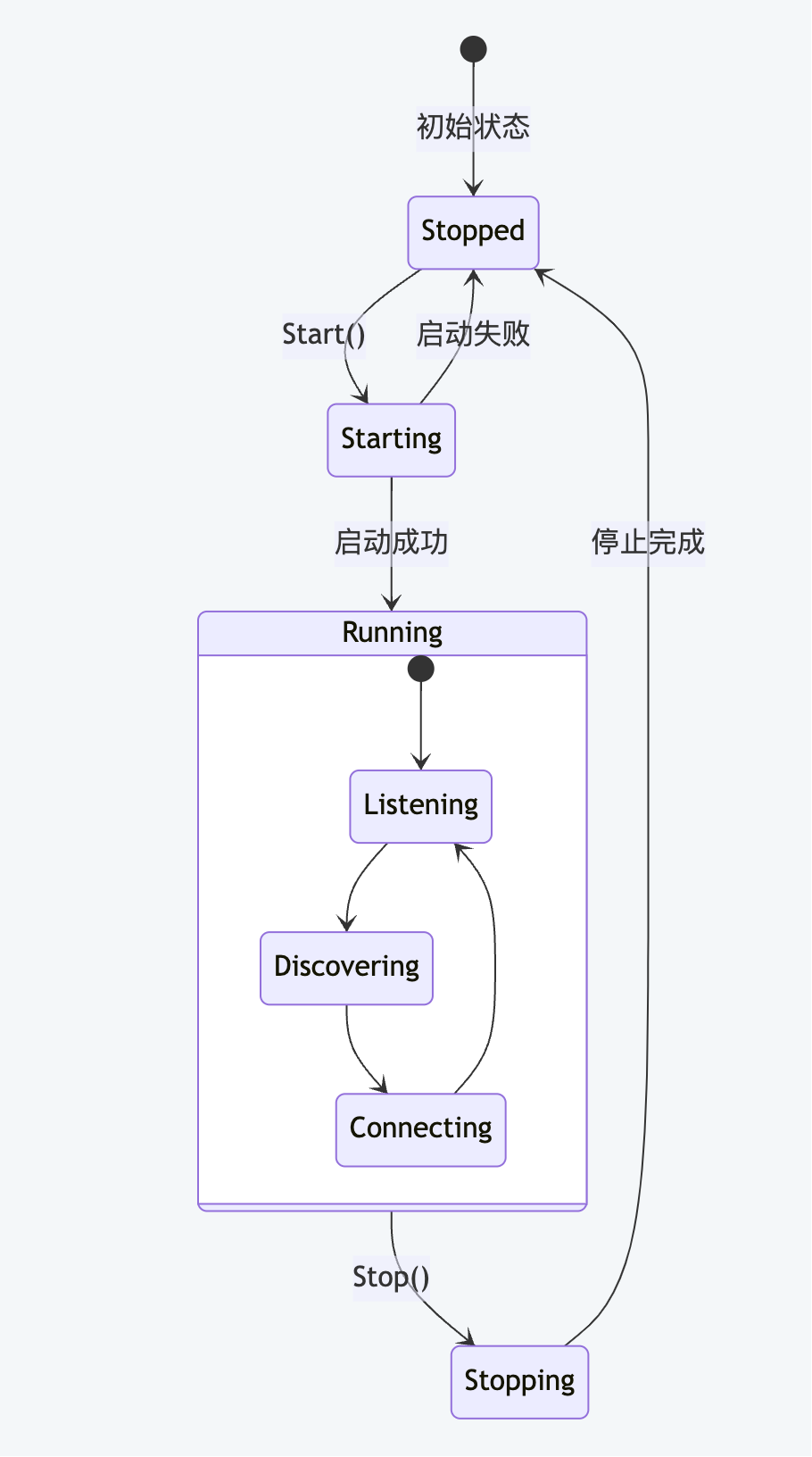 Concurrency control strategyA four-layer concurrency control mechanism is adopted: mutex locks protect key states, channels implement asynchronous communication, waiting groups manage the coroutine life cycle, and context controls timeout and cancellation. This layered design avoids excessive synchronization and improves concurrency performance by giving priority to the lock-free mode of channels. Event channel designAn event processing system is built using a channel-based event-driven architecture. Seven dedicated channels are designed to handle different types of events: the quit channel is responsible for the delivery of graceful shutdown signals, the addtrusted and removetrusted channels manage the dynamic addition and removal of trusted nodes, the peerOp channel handles various node operation requests, the delpeer channel handles node disconnect events, and the checkpointPostHandshake and checkpointAddPeer channels handle post-handshake checkpoints and node add checkpoints respectively. All these event channels are converged into the main event loop Server.run for unified scheduling and processing, forming an efficient event distribution mechanism to ensure that the system can respond to various network events in a timely manner and perform corresponding status updates and resource management. 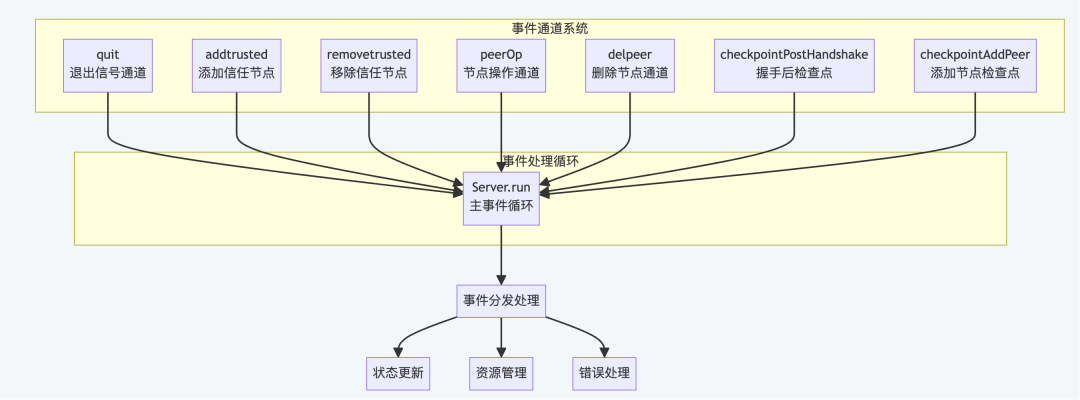 2.2 Connection management mechanismTCP listener implementation principleThe TCP listener adopts asynchronous listening mode and continuously accepts new connections in independent goroutine to avoid blocking the main thread. The system performs IP restrictions and pre-checks on the number of connections before establishing a connection, and controls the maximum number of concurrent connections through the semaphore mechanism to prevent resource exhaustion. Each new connection is handled asynchronously in a separate coroutine, ensuring that the listening loop is not blocked by a single connection. When an error occurs during the listening process, the system will automatically clean up resources and exit. It also supports a graceful shutdown mechanism that can stop accepting new connections and properly handle existing connections. In addition, the listener will dynamically update the network address information of the local node to ensure the real-time and accuracy of the node information. Connection establishment process principleThe connection establishment process consists of five key stages:
Connection pool managementConnection pool management adopts refined control strategy:
Connection status maintenanceEach connection has complete status tracking and lifecycle management:
 2.3 Peer node managementPeer object life cyclePeer has a complete life cycle management: starting from creating a Peer object based on an established connection and initializing the channel state, to starting all supported protocol processors to establish a message processing loop, to processing protocol messages during runtime, maintaining connection status and monitoring connection health, and finally shutting down the protocol processor gracefully and cleaning up resources to disconnect. The entire design ensures concurrency security in a multi-coroutine environment through channels and waiting group mechanisms, and implements error isolation between protocols to prevent single protocol failures from affecting the operation of other protocols. It also has automated coroutine life cycle and resource management capabilities, and provides a complete connection event subscription notification mechanism. 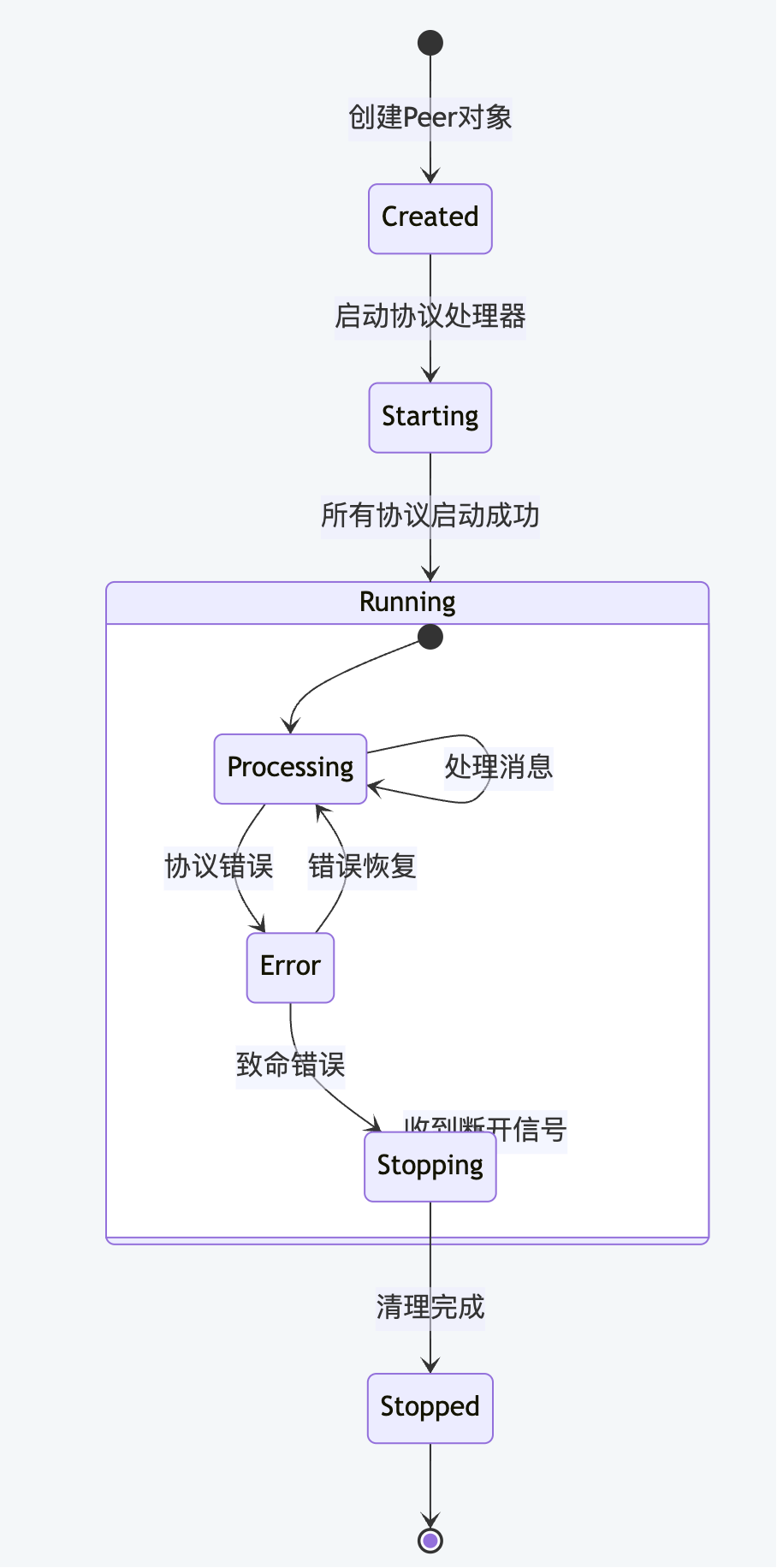 Node working example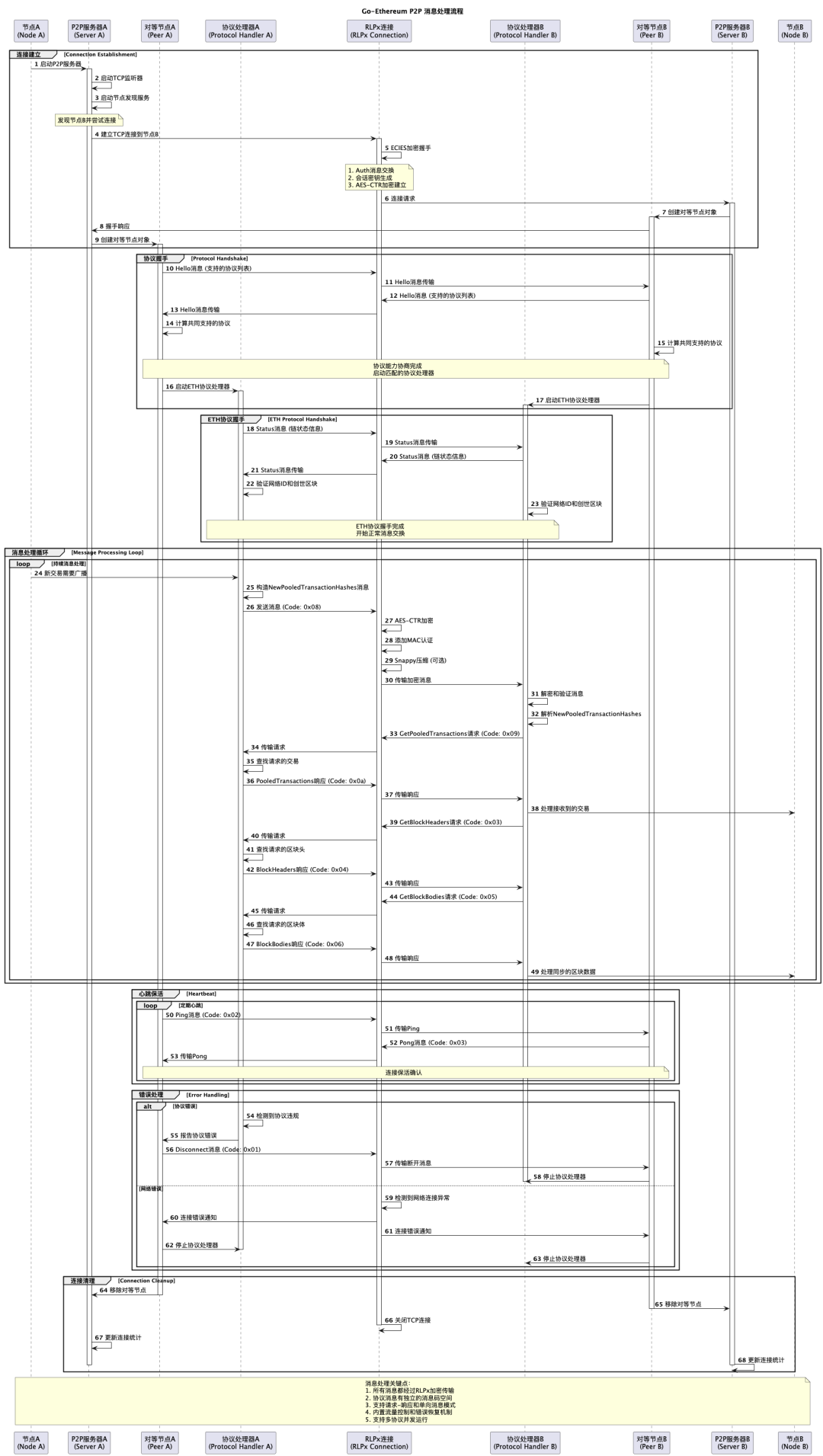 2.4 Protocol multiplexingProtocol registration mechanismThe protocol registration mechanism implements modular management of protocols through standardized protocol interface definitions. Each protocol contains core attributes such as name, version, number of message types, running functions, and node information. The system manages all registered protocols in a unified manner through the protocol registry, and publishes the list of supported protocols to peer nodes through the capability declaration mechanism during the handshake phase. Message routing implementationMessage routing implements protocol isolation through the message code offset mechanism. Each protocol is allocated an independent message code space, and the router distributes the message to the corresponding protocol processor according to the message code range. At the same time, each protocol processor has independent input channels, write control and error handling mechanisms to ensure complete isolation and concurrency safety between protocols. Protocol version negotiationThe protocol version negotiation adopts the best matching strategy. The system first sorts the protocol capabilities of both parties by name and version, and then matches them one by one to find a commonly supported protocol version. The local protocol list is compared with the remote capability list. For protocols with matching names, version compatibility is checked. If they are compatible, a processor is created and a message code offset is assigned. If they are not compatible, an available version is selected. Unmatched protocols are skipped directly until all protocols are checked and negotiated. Chapter 3: In-depth analysis of node discovery mechanism3.1 Discovery v4 protocol implementationKademlia DHT algorithm principleKademlia is a distributed hash table algorithm based on XOR distance metric, and Go-Ethereum adopts its core idea to build a node discovery network. The core of the algorithm is to assign a 256-bit unique identifier to each node in the network and calculate the "distance" between nodes through the XOR operation. Node search algorithm process: 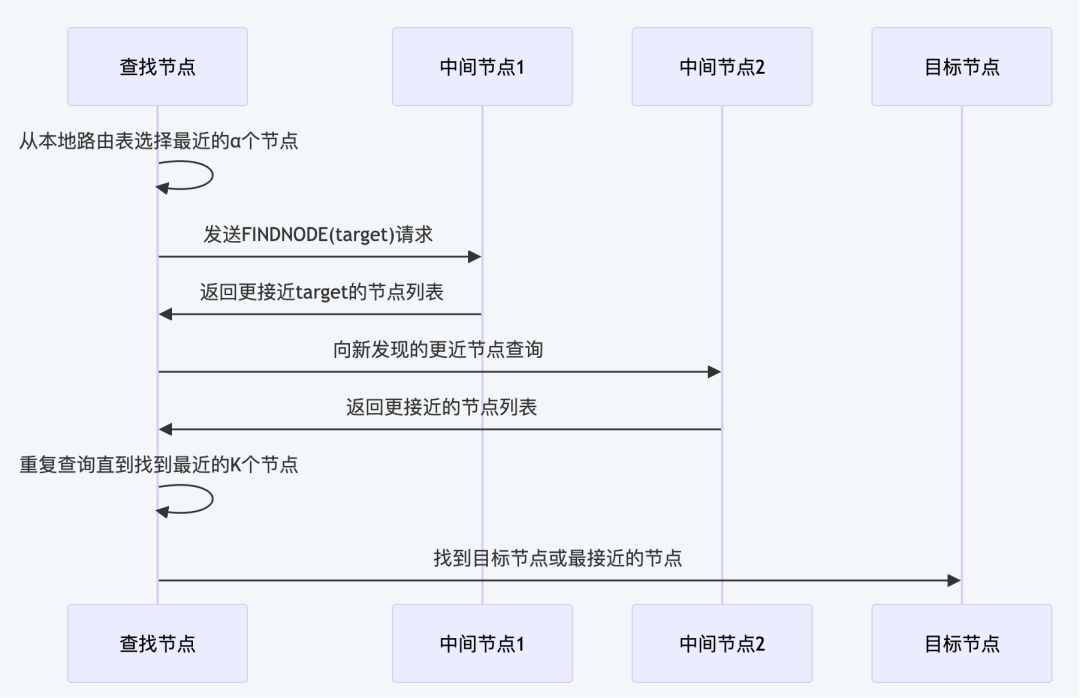 The search algorithm adopts an iterative method, each time selecting α unqueried nodes (usually α=3) closest to the target, and sending query requests in parallel. By continuously narrowing the search range, the K nodes closest to the target are finally found. Routing table maintenance mechanism:
This design makes the Kademlia network have good self-organizing capabilities and fault tolerance, and can maintain stable routing performance in an environment where nodes dynamically join and leave. UDP communication mechanismDiscovery v4 uses the UDP protocol for communication and supports four message types:
3.2 Discovery v5 protocol evolutionENR (Ethereum Node Records) systemDiscovery v5 introduces the ENR recording system to provide structured node information: type Record struct {Comparison between ENR and enodeIn Discv4, nodes use the enode URL format (enode://
topic discovery mechanismDiscovery v5 introduces a topic-based node discovery mechanism that allows nodes to be classified and discovered based on specific service or protocol types. This mechanism is particularly suitable for multi-protocol environments such as Ethereum 2.0. Topics enable precise node classification and finding by coordinating the core aspects of the work:
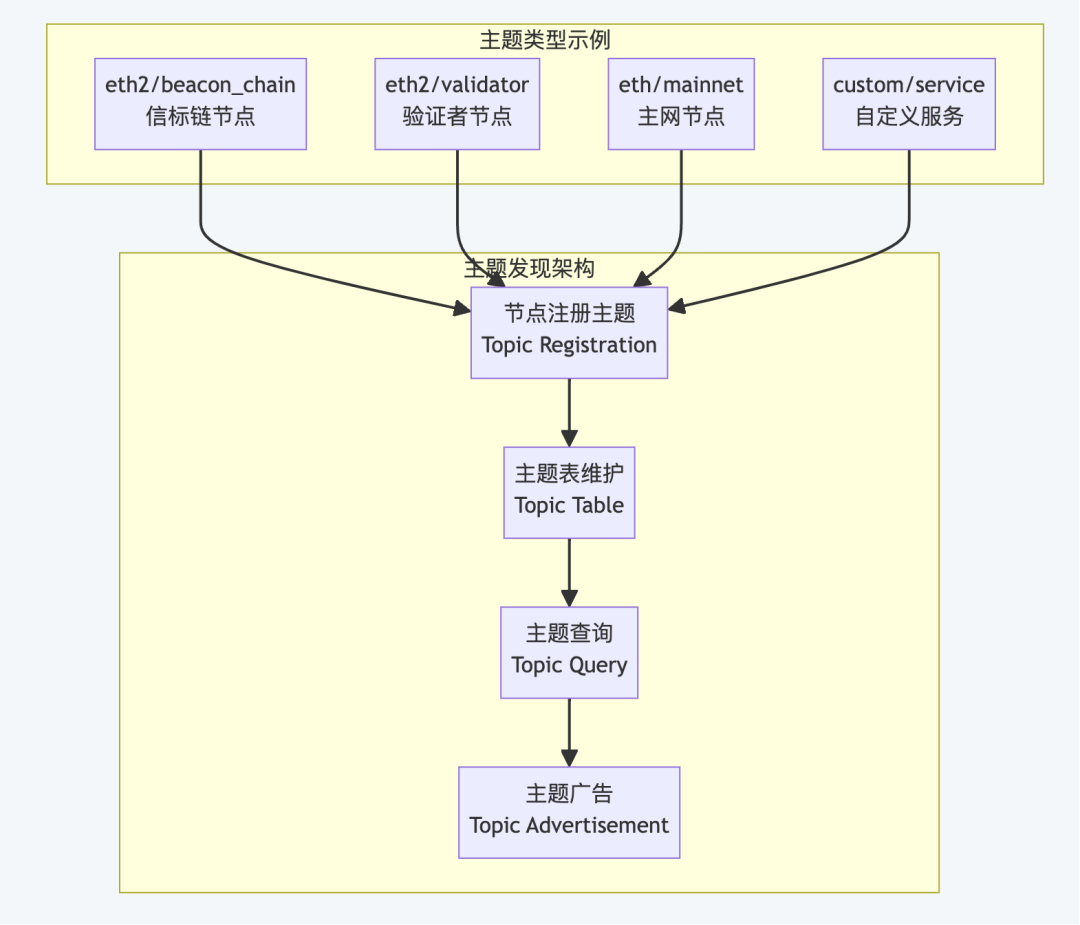 Topic discovery implementation mechanismThe topic discovery mechanism ensures efficient and flexible service discovery:
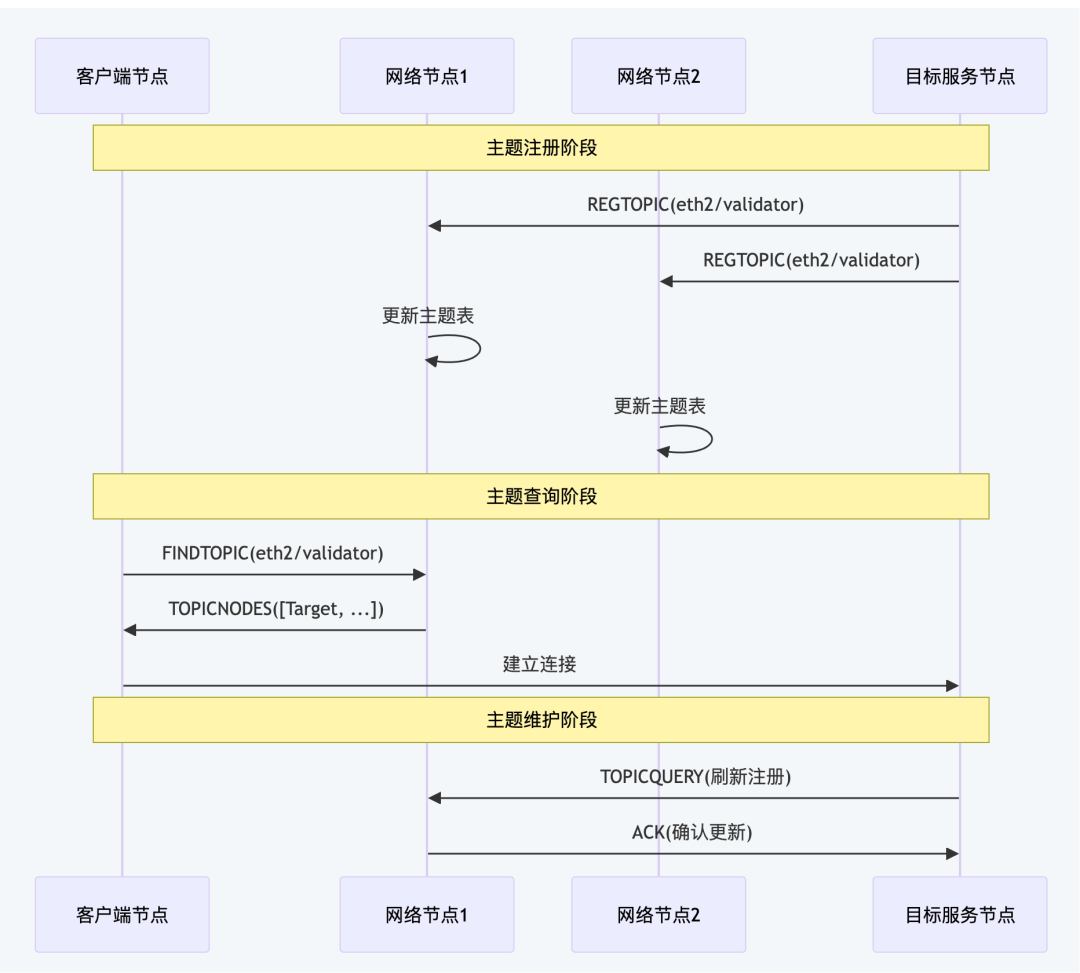 This topic discovery mechanism provides the Ethereum network with more accurate node discovery capabilities, and is especially suitable for scenarios that require specific service types of nodes, such as validator discovery, shard network construction, etc. 3.3 DNS Discovery ProtocolEIP-1459 standard implementationThe DNS discovery protocol is based on the EIP-1459 standard and implements decentralized node discovery through standard DNS infrastructure. The core of the protocol is the DNS client, which integrates several key components to ensure efficient and reliable node discovery. The implementation mechanism of DNS query adopts the standard TXT record query method: the system combines the node hash value and the domain name to form a complete DNS query name, queries the corresponding TXT record through the standard DNS parser, and then traverses all the returned TXT records to try to parse them into valid node entries. Once a valid entry that meets the verification scheme is found, it will be returned immediately. If all records cannot be parsed, a query failure error will be returned. This design makes full use of the existing DNS infrastructure to achieve high availability and globally distributed node discovery services. tree structure designDNS discovery uses a Merkle tree structure to organize node information, and builds a hierarchical node discovery system through different types of entries: DNS tree entry type description:
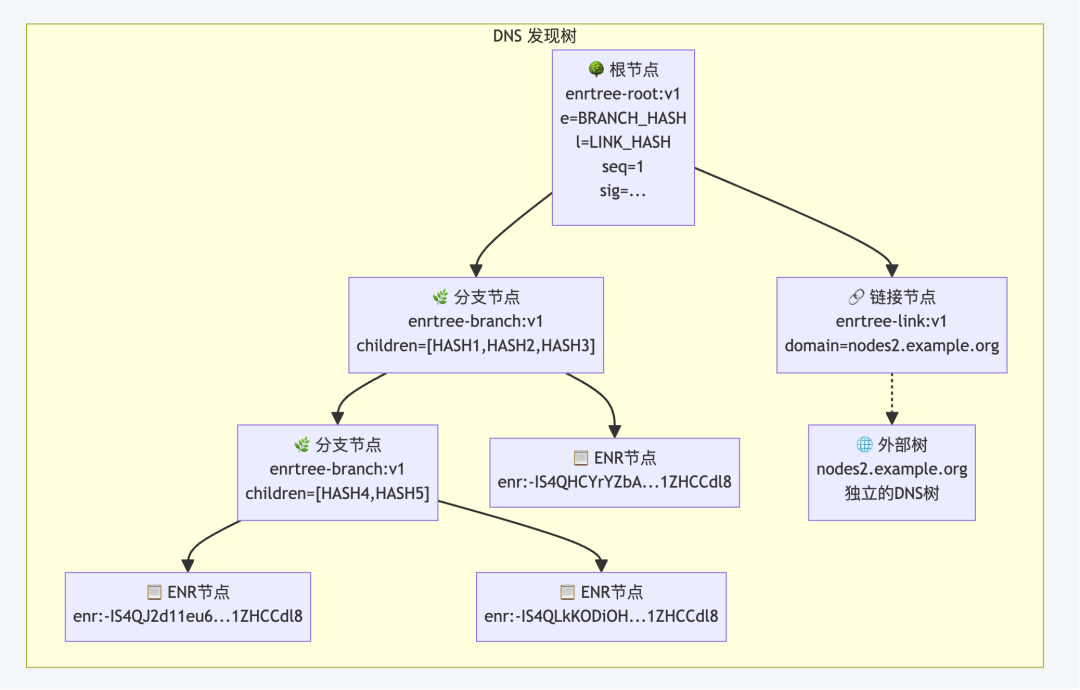 3.4 Node mixing and schedulingFairMix node mixerFairMix implements a fair node mixer that obtains nodes by polling multiple discovery sources (such as Discovery v4, v5, DNS, etc.) to ensure that each discovery source has an equal opportunity to provide nodes and avoid a certain source from monopolizing the node discovery process, thereby achieving load balancing and fair scheduling of discovery sources. Boot node mechanismThe boot node provides network entry for new nodes: var MainnetBootnodes = []string{Node type
Connection priority
Chapter 4: RLPx Encrypted Transmission Protocol4.1 RLPx protocol stack designprotocol hierarchyThe RLPx protocol stack adopts a layered design, with each layer responsible for specific functions: 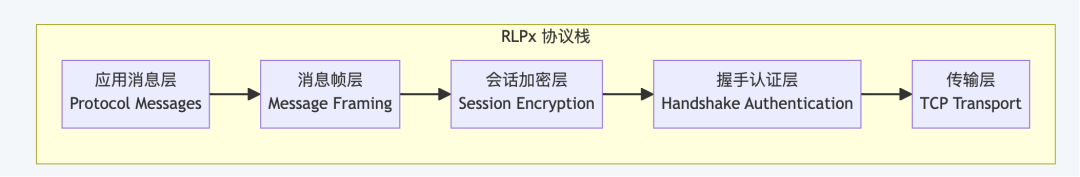 4.2 Working mechanism
4.3 Message frame format and processingFrame structure designThe RLPx message frame contains two parts: header and data: 消息帧格式:AES-CTR stream encryptionUse AES-CTR mode for stream encryption. The message frame reading adopts the "read-verify-decrypt" security process: first read the 32-byte frame header (16-byte encryption header + 16-byte MAC), verify the integrity of the header MAC and then decrypt to obtain the frame size. ; Then read the aligned frame data and MAC verification code according to the frame size to verify the integrity of the frame data. ; Finally, the frame data is decrypted and padding is removed, returning the original message content. This double MAC verification (header and data are verified separately) combined with complete encryption ensures the security and integrity of message transmission. MAC message authenticationUse HMAC to ensure message integrity: first write the input data to the hash function and generate a seed value; Then use AES to encrypt the seed and XOR the result with the input data. ; Finally, the XOR result is AES encrypted again to generate a 16-byte MAC value. Snappy compression optimizationSupport Snappy compression to reduce network transmission Chapter 5: Application protocol layer implementation5.1 In-depth analysis of ETH protocolThe ETH protocol is the main application protocol of the Ethereum network and is responsible for the synchronization and dissemination of blockchain data. The protocol has evolved through multiple versions, and currently mainly uses the ETH/68 and ETH/69 versions to provide complete blockchain data exchange capabilities for full nodes. 5.2 SNAP protocol status synchronizationThe SNAP protocol is specifically designed to solve the problem of state synchronization efficiency. Allow nodes to directly download the latest status snapshot, greatly reducing synchronization time. 5.3 LES light client protocolThe LES (Light Ethereum Subprotocol) protocol provides a lightweight solution for resource-constrained devices to participate in the Ethereum network. Allows light clients to verify transactions and query status without downloading the full blockchain. 5.4 Protocol extension and customizationGo-Ethereum provides a complete protocol extension framework, allowing developers to implement custom protocols according to specific needs. It provides a strong technical foundation for the innovation of blockchain applications. SummarizeGo-Ethereum P2P The network has been deeply optimized specifically for blockchain scenarios: it efficiently handles block propagation and transaction synchronization through event-driven architecture, uses multi-layer security protection to resist malicious node attacks, uses refined concurrency control to achieve high-performance processing of large-scale node networks, uses state machine management to ensure the reliability of complex network state transitions, establishes a complete resource management mechanism to support long-term stable operation of nodes, and uses multiple fault-tolerant mechanisms to respond to frequent node changes and network abnormalities to ensure the self-healing ability and continuous stable operation of the entire blockchain network. This article can only attempt to explain part of the content. |